You can use firewall softwares to make certain that only licensed users are enabled to access or transfer information. These procedures are typically used as component of an identification and also accessibility monitoring (IAM) service as well as in mix with role-based accessibility controls (RBAC).
Security secures your data from unauthorized access also if data is swiped by making it unreadable. Endpoint defense software generally allows you to check your network border and also to filter website traffic as needed.
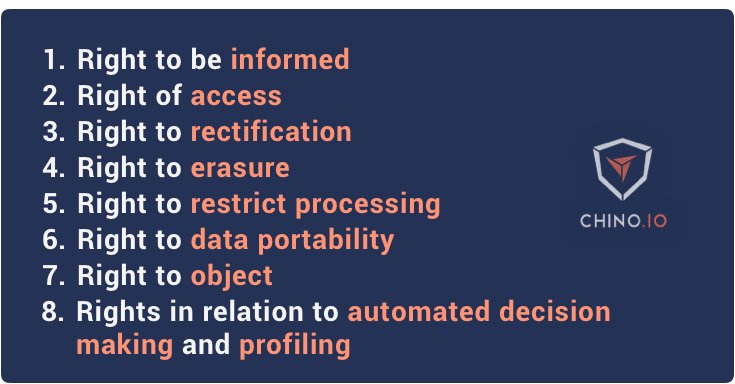
This can be done after data is processed and also evaluated or periodically when information is no much longer appropriate. Eliminating unneeded data is a requirement of numerous compliance regulations, such as GDPR.
The Single Strategy To Use For Aws S3 Backup
Developing policies for information privacy can be tough however it's not difficult. The adhering to finest methods can assist you make sure that the policies you create are as reliable as possible. Component of making certain data privacy is comprehending what data you have, exactly how it is dealt with, as well as where it is saved.
For example, you need to specify exactly how regularly data is checked for as well as how it is classified once located. Your privacy policies must clearly outline what protections are required for your various information personal privacy degrees. Plans should additionally consist of processes for auditing protections to make sure that options are used properly.
If you gather greater than what you require, you enhance your responsibility and can produce an unnecessary concern on your protection groups. Minimizing your information collection can likewise assist you save money on data transfer and also storage. One means of achieving this is to make use of "validate not shop" structures. These systems make use of third-party information to confirm users and also get rid of the need to shop or transfer customer information to your systems.
How Protection Against Ransomware can Save You Time, Stress, and Money.
Showing this, GDPR has made user consent a crucial aspect of data usage and also collection. Having clear customer alerts laying out when data is collected as well as why.
Data mobility is an important requirement for many modern IT companies. It suggests the capacity to relocate information in between various environments and software applications. Extremely commonly, information transportability indicates the capability to move information between on-premises information centers as well as the general public cloud, and also between different cloud companies. Data mobility additionally has lawful implicationswhen information is stored in various countries, it goes through different regulations and also laws.
Traditionally, data was not mobile and it called for huge initiatives to move huge datasets to an additional atmosphere. Cloud data movement was likewise very challenging, in the early days of cloud computing.
Examine This Report on Aws Backup
This makes it hard to relocate data from one cloud to another, and produces vendor secure. Significantly, companies are looking for standardized ways of saving as well as taking care of information, to make it mobile throughout clouds. Smart phone defense describes measures developed to shield delicate info stored on laptops, mobile phones, tablets, wearables and also various other mobile gadgets (EC2 backup).
In the contemporary IT setting, this is an essential aspect of network safety. There are lots of mobile information security devices, designed to shield mobile phones as well as information by recognizing hazards, producing backups, as well as preventing dangers on the endpoint from reaching the corporate network. IT team usage mobile data protection software program to allow safe and secure mobile access to networks and systems.
Ransomware is a kind of malware that secures customer information as well as requires a ransom money in order to launch it. New sorts of ransomware send out the data to assailants before encrypting it, enabling the attackers to obtain the organization, endangering to make its sensitive information public. aws backup. Back-ups are an effective defense against ransomwareif an organization has a recent duplicate of its data, it can recover it and regain access to the information.
Getting My Rto To Work
![]()
At this stage ransomware can infect any kind of connected system, consisting of backups. When ransomware spreads out to back-ups, it is "game over" for information security approaches, because it becomes impossible to restore the encrypted data. There are numerous approaches for preventing ransomware and particularly, preventing it from infecting backups: The easiest method is to use the old 3-2-1 back-up rule, keeping 3 duplicates of the information on 2 storage space media, among which is off facilities.
Storage suppliers are using unalterable storage, which makes sure that information can not be customized after it is saved. Learn exactly how Cloudian safe storage can assist secure your back-ups from ransomware. Huge companies have several datasets stored in different areas, and several of them may duplicate information between them. Replicate information develops several problemsit enhances storage space costs, creates inconsistencies and operational concerns, and also can additionally lead to safety and security and compliance difficulties.
It is no use safeguarding a dataset as well as ensuring it is compliant, when the information is duplicated in one more unidentified area. aws backup. CDM is a type of service that finds replicate information and helps handle it, contrasting similar information as well as allowing managers to erase unused copies. Catastrophe healing as a service (DRaa, S) is a handled solution that offers an organization a cloud-based remote disaster recuperation site.
Data Protection Fundamentals Explained
With DRaa, S, any kind of size company can duplicate its regional systems to the cloud, as well as conveniently recover operations in case of a catastrophe. DRaa, S services take advantage of public cloud framework, making it possible to save several duplicates of facilities and information across numerous geographical locations, to boost resiliency - protection against ransomware. Data protection calls for powerful storage space technology.